For a hacker, chaos isn’t a pit, Chaos is ladder this idea is explained during this article with the assistance of some hacker and their terms.
“To better describe hacking, one needs to first understand hackers.”
Who may be a Hacker?
A hacker is a private who uses computer, networking or other skills to beat a technical problem. The term hacker may ask anyone with technical skills, but it often refers to an individual who uses his or her abilities to realize unauthorized access to systems or networks so as to commit crimes. A hacker may, for instance , steal information to harm people via fraud , damage or bring down systems and, often, hold those systems hostage to gather ransom.
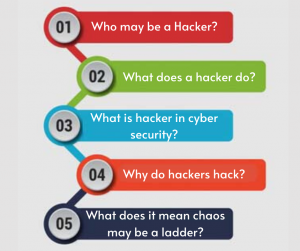
What does a hacker do?
Computer hackers are unauthorized users who forced an entry computer systems so as to steal, change or destroy information, often by installing dangerous malware without your knowledge or consent. Their clever tactics and detailed technical knowledge help them access the knowledge you actually don’t need them to possess.
“Most hackers are young because children tend to be adaptable. As long as you remain adaptable, you’ll always be an honest hacker.”
? Emmanuel Goldstein
What is hacker in cyber security?
A hacker is a private who uses computer, networking or other skills to beat a technical problem. The term hacker may ask anyone with technical skills, but it often refers to an individual who uses his or her abilities to realize unauthorized access to systems or networks so as to commit crimes
Related Product:- Certified Ethical Hacker | CEH Certification
Why do hackers hack?
Motives. Four primary motives are proposed as possibilities for why hackers plan to forced an entry computers and networks. First, there’s a criminal gain to be had when hacking systems with the precise purpose of stealing mastercard numbers or manipulating banking systems.
What does it mean chaos may be a ladder?
The climb may be a metaphor for achieving power, and therefore the ladder (chaos) is how Littlefinger climbs. When things are in disarray it allows him to control in order that he’s ahead. Chaos means the good houses overlook his birth, because they have him.
Also Read:- what’s Ethical Hacking? & sorts of Hacking
Hacking is an attempt to exploit a computer system or a private network inside a computer. Simply put, it is the unauthorised access to or control over computer network security systems for some illicit purpose.
Infosavvy CEH certification training course provides you the hands-on training required to master the techniques hackers use to penetrate network systems and fortify your system against it. This ethical hacking course is aligned with the latest CEHv10 training and certification with Infosavvy in Mumbai Location and accreditation by EC-COUNCIL will adequately prepare you to increase skills.
“Chaos isn’t a pit. Chaos may be a ladder.”
-Petyr Baelish
Chaos isn’t a pit. Chaos may be a ladder. many that attempt to climb it fail, and never get to undertake again. the autumn breaks them. and a few are given an opportunity to climb, but refuse. They hold close the realm, or love, or the gods…illusions. Only the ladder is real. The climb is all there’s . But they’ll never know this. Not until it’s too late.
What hackers do is find out technology and experiment with it in ways many of us never imagined. They even have a robust desire to share this information with others and to elucidate it to people whose only qualification could also be the will to find out .
Learn CEH & Think like hacker
- What is Ethical Hacking? & Types of Hacking
- 5 Phases of Hacking
- 8 Most Common Types of Hacker Motivations
- What are different types of attacks on a system
- Scope and Limitations of Ethical Hacking
- TEN Different Types Of Hackers
- What is the Foot-printing?
- Top 12 steps for Foot printing Penetration Testing
- Different types of tools with Email Foot printing
- What is “Anonymizer” & Types of Anonymizers
- Top DNS Interrogation Tools
- What is SNMP Enumeration?
- Top vulnerability scanning tools
- Information Security of Threat
- Foot printing tools:
- What is Enumeration?
- Network Security Controls
- What is Identity and Access Management?
- OWASP high TEN web application security risks
- Password Attacks
- Defend Against Key loggers
- Defend Against Spyware
- Covering Tracks
- Covering Track on Networks
- Everything You Need To Know About Sniffing – Part 1
- Everything You Need To Know About Sniffing – Part 2
- Learn more about GPS Spyware & Apparatuses
- Introduction of USB Spyware and It’s types
- 10 Types of Identity Theft You Should Know About
- Concepts of Denial-of-Service Attack & Distributed Denial of Service Attack
- Most Effective Ways to Overcome Impersonation on Social Networking Site’s Problem
- How Dynamic Host Configuration Protocol (DHCP) Works
- DHCP Request/Reply Messages
- DHCP Starvation Attack
- Rogue DHCP Server Attack
- IOS Switch Commands
- Web Server Concept
- Web Server Attacks
- Web Server Attack Tools
- Web Server Security Tools
- 6 Quick Methodology For Web Server Attack
- Learn Skills From Web Server Foot Printing / Banner Grapping
- The 10 Secrets You Will Never Know About Cyber Security And Its Important?
- Ways To Learn Finding Default Content Of Web Server Effectively
- How will Social Engineering be in the Future
- Understand The Background Of Top 9 Challenges IT Leaders Will Face In 2020 Now
- Learning Good Ways To Protect Yourself From Identity Theft
- Anti-phishing Tools Guide
- Top 5 Firefox extensions for Secure Browsing
- Top 12 Common Cybersecurity Analyst Interview Questions with Answers
This Blog Article is posted by
Infosavvy, 2nd Floor, Sai Niketan, Chandavalkar Road Opp. Gora Gandhi Hotel, Above Jumbo King, beside Speakwell Institute, Borivali West, Mumbai, Maharashtra 400092
Contact us – www.info-savvy.com